Office 365 Activities API - Example Output
Yesterday CrowdStrike published details of the 'Office 365 Activities API' which is an extremely useful source of evidence for investigations, especially in cases of Business Email Compromise. The detailed post can be read here. Included was a Python module which allows one to pull the discussed data from O365.
I also put out a recent blogpost commenting on how much research goes unshared and how I feel it is important that companies and individuals share resources, tools and research so as to further the whole field. In the mean time I had been working with a test O365 account to generate some Activity API output for colleagues and industry friends who may not have seen it before and who don't necessarily have access to an O365 account for testing, I would be a little hypocritical if I didn't share this with the wider community so here goes.
Incidentally if you want to jump to the output data without reading all my waffle, it can be found here.
The Setup
My Office365 test environment is a single user tenant at the time of testing so my only user is also an admin user. This poses some limitations but I will be expanding testing with the addition of a further account shortly. In the mean time I have used two Office365 accounts which I have access to, one where I am an admin and one where I am a user. In both cases a user is able to access the Activities API data as it relates to their own account.
The Procedure
My testing procedure comprised of logging into an O365 mailbox and performing actions which I thought would generate some interesting log data for a sample output. I actually performed these actions across two accounts and then merged the log so there was only a single file to review.
The accounts were both configured to be accessible from a mobile device (Android mail configured with exchange settings). No effort was made to generate traffic from a mobile device, all activity was performed via the browser, however it is possible that this may have impacted the resultant logs.
After downloading the python module from the CrowdStrike GitHub the first task was to generate some known account activity. The following steps were performed:
--Account 1--
2018-06-20T07:36:00 - Open Outlook.com (autologin)
2018-06-20T07:37:00 - Sign out
2018-06-20T07:37:30 - Sign in
2018-06-20T07:38:00 - Approve sign in request via android app
2018-06-20T07:38:30 - Opt to "stay signed in"
2018-06-20T07:39:10 - Open 'Outlook' web app
2018-06-20T07:39:40 - open email in viewing pane
2018-06-20T07:40:00 - open email in jump out window
2018-06-20T07:40:25 - select [new (+)] to compose new email
2018-06-20T07:41:07 - send email
2018-06-20T07:41:28 - open sent items
2018-06-20T07:42:00 - open sent email message in viewing pane
2018-06-20T07:42:30 - press delete on sent email
2018-06-20T07:42:55 - expand folders view
2018-06-20T07:43:25 - right click and select delete all from deleted items
2018-06-20T07:44:00 - open Junk email
2018-06-20T07:44:44 - press settings
2018-06-20T07:45:45 - close settings
2018-06-20T07:46:46 - right click message and 'create rule'
2018-06-20T07:47:37 - save rule
2018-06-20T07:48:00 - select 'OK'
2018-06-20T07:49:15 - search for and open 'inbox rules'
2018-06-20T07:49:48 - press new
2018-06-20T07:50:15 - receive alert and open it
2018-06-20T07:50:42 - select investigate and Security & Compliance center opens
2018-06-20T07:51:17 - return and cancel rule creation
2018-06-20T07:51:55 - Sign Out
2018-06-20T08:44:15 - Sign In
--Account 2--
2018-06-20T08:44:25 - Search for 'wire transfer'
2018-06-20T08:44:25 - Search for 'banking'
2018-06-20T08:44:25 - Search for 'bacs'
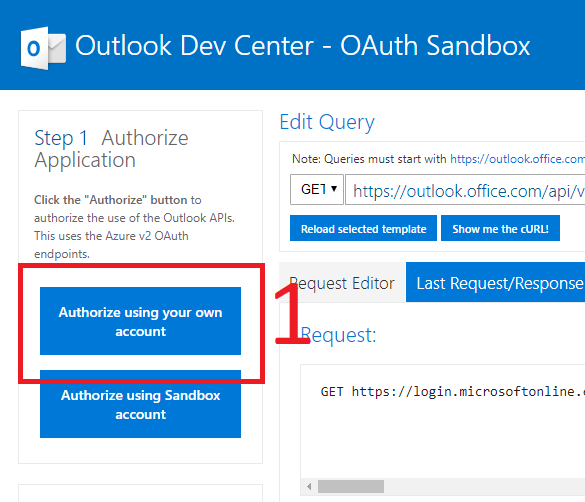
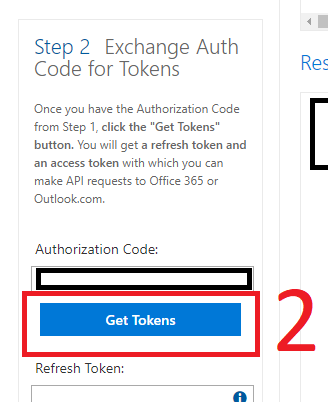
The next step was to acquire an OAuth Token, for the purposes of testing I employed the Outlook Dev Center - OAuth Sandbox to generate the appropriate OAuth token. For those who are not familiar the procedure is as follows:
- Select 'Authorise using your own account:
- Authenticate with the relevant account credentials:
- Copy Out the Access token that appears in the 'Access Token' box:
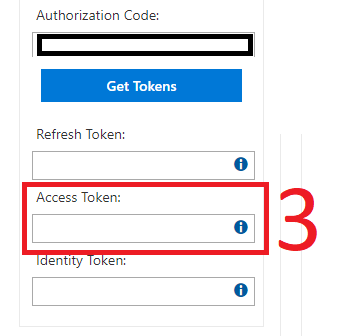
Note that the Access Token is a long string including characters which may preclude the 'double click to select call' so 'Ctrl-A'ing while within the text box is your best bet.
The copied string can then be added to the --Token variable when using CrowdStrike's retriever.py in the below command to dump the full history of activities for a user:
python retriever.py --user test@address.com --output activities.csv --token \[OAuth Access Token String]
The above command worked for me but I have limited activity on my test account, more targeted extracts may be needed for genuine accounts.
My test output should be reviewed in conjunction with the list of activities performed, as above. Note that the times are approximate on account of me being human. The logs have been modified to replace my Login IP with '175.45.176.123' and the account addresses have been modified to 'test@address.com'.
Without further ado, the resulting csv output from my testing is available here.